I know, I haven’t been on here in some time. Life has felt a bit more nuts and bolts, focusing on execution rather than going above and beyond. I haven’t been feeling terribly creative or ready to do any research in the pursuit of knowledge. That’s really what this is for which explains why I haven’t been able to expend much time on this. Regardless, I really need to try doing a little here and there just to justify this being up and running.
For this edition, I’m interested in digging into a bit of a topic even if that doesn’t result in the full watching, reading, listening list. That topic is the Iranian uranium enrichment facility, Natanz. The Iranian facility has a bit of a history, acting as the crown jewel in Iranian nuclear ambitions. For this reason, it’s been a central focus of the international community’s handwringing over Iranian nuclear ambitions. There’s been a string of assassinations targeting the top scientists in the Iranian nuclear program that were pinned on Israel. Aside from this there were more overt actions to target the Natanz facility in particular.
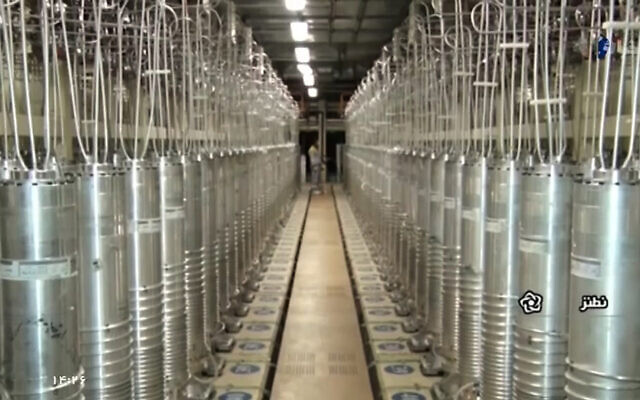
The most notable of this is the Stuxnet malware which was only uncovered in 2010 after a Belarusian contractor had initially detected a suspect file on a client computer in Iran. While we sometimes get swept up in hyperbole, it doesn’t seem excessive to say that Stuxnet was the first example of causing physical harm with code. Prior to that, cyberspace has mostly been limited to stealing money or intellectual property, both damaging in their own right but not the same as physical harm. Stuxnet really crossed the Rubicon. Stuxnet was incredibly sophisticated. It used multiple “zero day” exploits in the software and hardware that managed the nuclear facility. Even with that, it was exceptionally cautious. Centrifuges were spun up ever so slightly more or less than it reported to those monitoring. This was to increase wear on the internal components, resulting in breakages, taking the centrifuges out of production and wearing down capability. Eventually, the detection led to a storm of dogged reporting and leaks that pointed to the United States and Israeli collaboration on Stuxnet, offering an alternative to Iran building a bomb or having to be bombed.

Jumping ahead to today, we saw a kinetic attack via what’s been reported as an explosive device targeting the power for the centrifuge arrays. Iran’s state media has reported that a “small explosive device” was planted by a man named Reza Karimi, a 43 year-old Iranian national who has since fled the country. Somehow, backup power to the facility was also cut which caused the centrifuges to shut down abruptly, effectively destroying them all. Iran hasn’t been very forthcoming about the scope of the damage, going so far as to say that Western media was overblowing it although experts assume that, based on the information available, the facility is likely to be stalled for roughly nine months. This doesn’t appear to follow the same structure as the Stuxnet attacks, relying on physical explosives rather than a cyberattack although I’m sure that we’ll hear some more about this over the coming weeks and months.
The sabotage itself is a bit of a tough pill to swallow with the timing appearing to intentionally drive a wedge in the upcoming negotiations between the US and Iran. The negotiations are starting in Vienna to work out a way for the US to ease sanctions while the US and Iran return to the Joint Comprehensive Plan of Action, commonly referred to as the JCPOA or the “Iran Nuclear Deal”. Iran has stated that its nuclear enrichment is going to rise to 60% purity, a huge jump from its previous peak of 20% purity. Of course, these factors will only complicate the pursuit of a peaceful solution between the United States and Iran although the likelihood of success in these negotiations were already fraught with distrust and reservations.
Further information
This is, of course, a very high level view of the history of Iran, Iran’s nuclear program, and Natanz. So where do you go to learn more about this? There are some great resources and dogged research to help make sense of the history of Stuxnet and this recent attack.
“Zero Days” by Alex Gibney
“Zero Days” is a great documentary that covers the history of the Stuxnet virus and the ripples that come from the Stuxnet attack. It presents the technological aspects in a really digestible manner and asks some difficult questions about what this means for war in the future. Similar to the way that the nuclear weapon was used in 1945, Stuxnet was a new type of weapon that prompts the need for a new doctrine. Unfortunately, we’re a bit tied up in confidentiality even though ample details have leaked to the press about the use of the Stuxnet. This is something that’s important to think about and will come to a head in the future.
Link: JustWatch
“Countdown to Zero Day” by Kim Zetter
Kim Zetter is a quintessential expert to follow on the topic of “cyber war” and her book “Countdown to Zero Day” is probably the single most detailed account of the Stuxnet attack on the Natanz facility. To read this book will require a bit of patience if you don’t have the technical background to go with it however I do think it’s worth the while if you’re interested in getting to the bottom of something wrapped in so much smoke and mirrors.
Link: Goodreads
Reporting on Recent Explosion
Once again following Kim Zetter, her piece at The Intercept is a fairly helpful primer on what we do and don’t know regarding the explosion and blackout that ground Natanz to a total shutdown. It’s not too hard to follow for non-technical folks and comes with the the right disclaimers to make sense of the whole thing.
Link: The Intercept
Closing
Til next time, I hope to have some more stuff like this with a bit of a stream of thoughts related to topics that are actually interesting. Hopefully this spearheads some research and learning as well. Related to this, I’m hoping to dig into “The Fall of Heaven” by Andrew Scott Cooper about that fall of Iran’s final Shah which looks to be a bit of an exciting historic read. Maybe I’ll find a way to also slug throw some audiobooks while also finishing off the Russell Shorto book, “Amsterdam”.